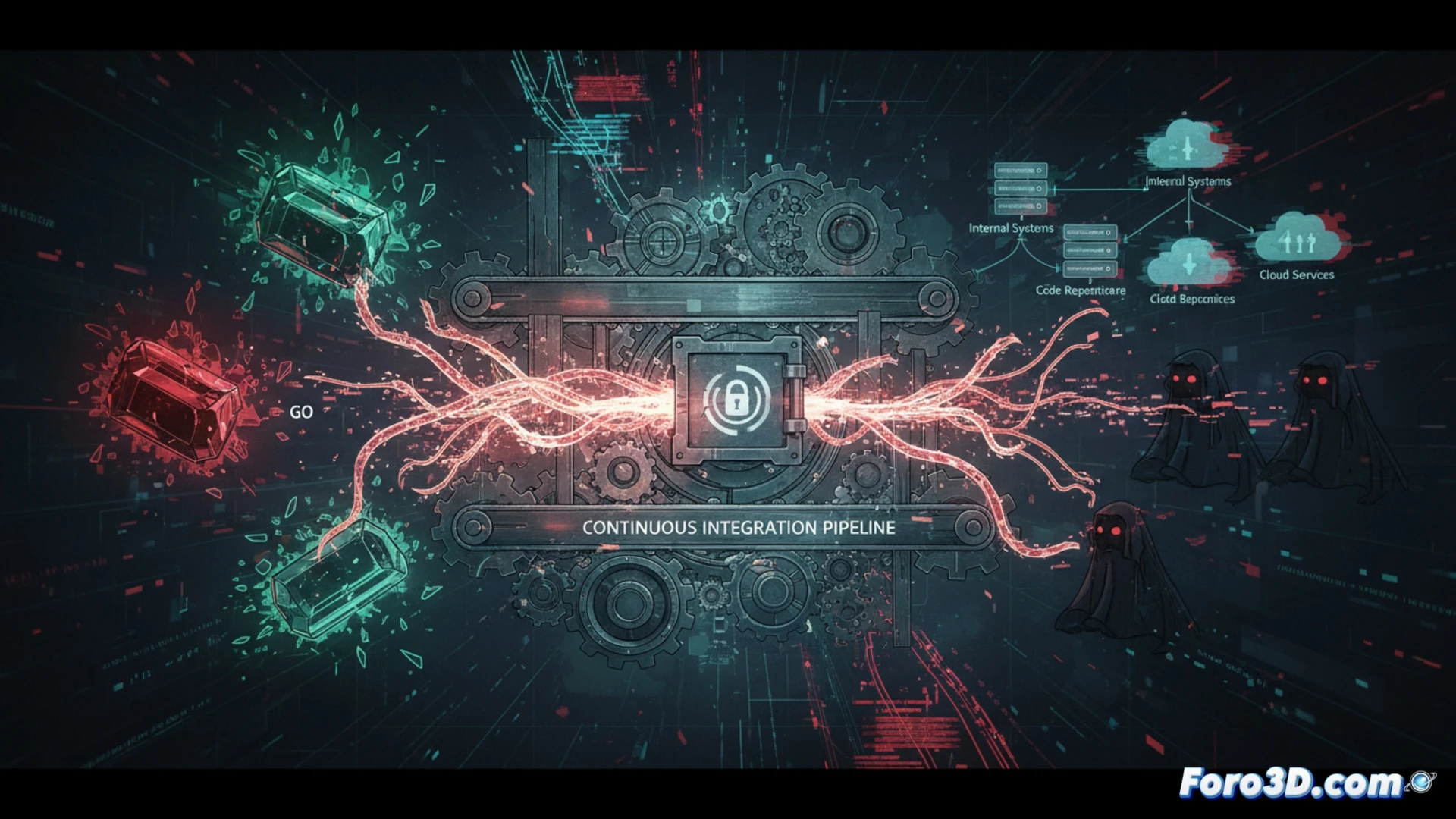
A new cyberattack campaign has been discovered by security researchers. Attackers publish malicious packages in repositories such as RubyGems and the Go module registry. By integrating them into projects, they execute hidden code that steals credentials stored in continuous integration environments, compromising internal systems and cloud services.
The attack mechanism: dependencies that betray 🛡️
Attackers inject malicious code into Ruby gems and Go modules, disguised as legitimate libraries. When a developer downloads and integrates them into their CI pipeline, the hidden code executes during the build phase. This malware extracts environment variables, access tokens, and stored SSH keys. The stolen credentials allow access to code repositories, internal systems, and cloud services without raising immediate suspicion.
The developer who trusted a gem and lost their pipeline ☕
Because, of course, what could go wrong when downloading a gem called ruby-utils-pro-max that promises to optimize your code by 500%. Attackers know that developers blindly trust public repositories. Now, in addition to reviewing logs and updating dependencies, it's time to pray that the gem you downloaded at 3 AM isn't stealing your credentials while you sip your coffee.