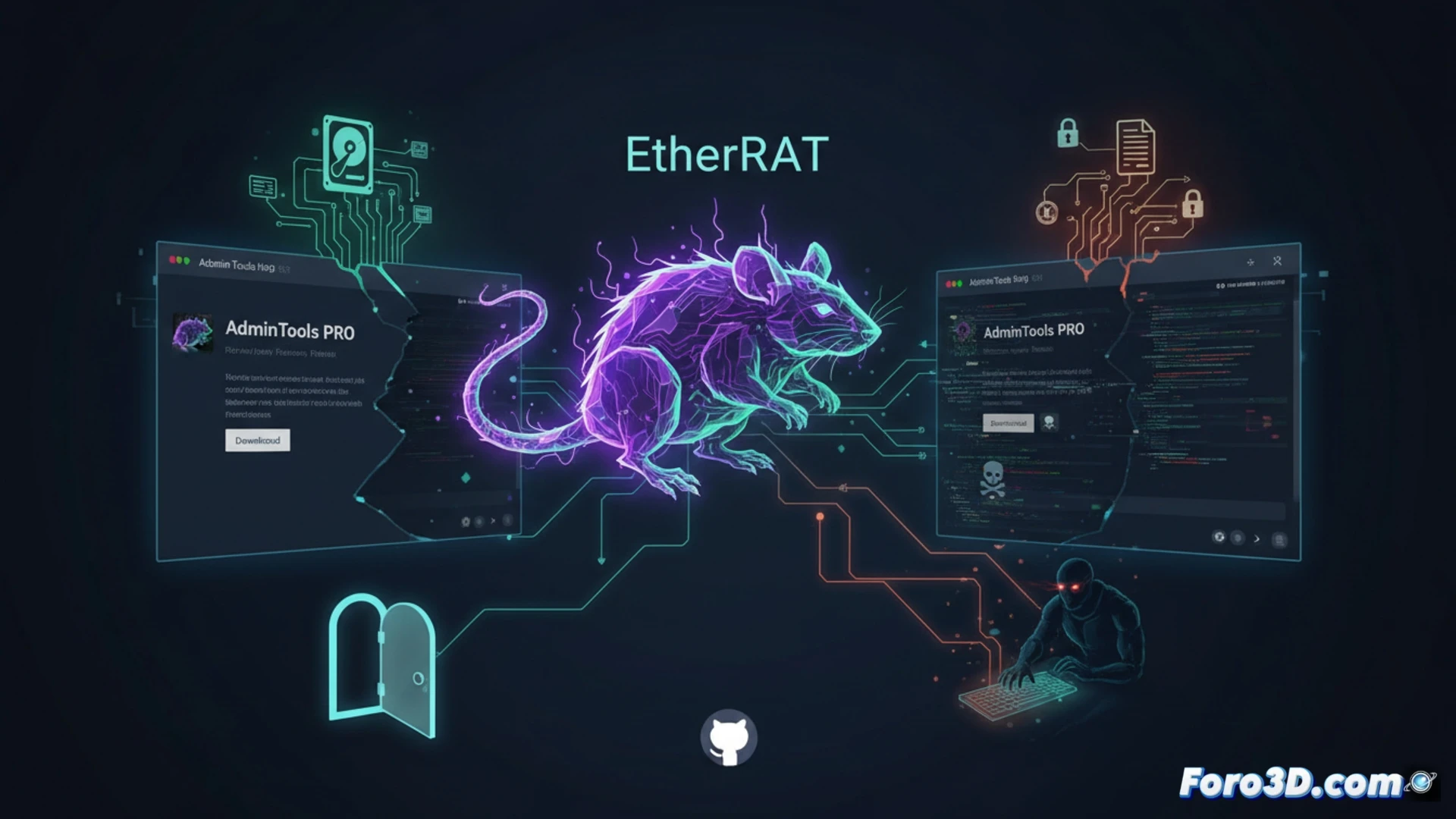
A new malware campaign, dubbed EtherRAT, is circulating online through websites that perfectly mimic legitimate administrative tools hosted on GitHub. Attackers create replicas of popular project pages, tricking IT professionals who trust the platform as a secure source. This remote access trojan allows cybercriminals to take control of the system, steal sensitive information, and execute commands without raising suspicion.
The modus operandi of the EtherRAT trojan 🕵️
EtherRAT operates like a typical remote access trojan, but its distribution is what sets it apart. Attackers clone legitimate GitHub repositories and slightly modify the URLs to appear authentic. Once downloaded, the malware establishes a connection with a command and control server, allowing the attacker to steal credentials, capture keystrokes, and move files. The infection goes unnoticed by running silently in the background, exploiting the trust placed in open-source tools.
When the GitHub clone is faker than a three-euro bill 😅
It turns out the old trick of making fake copies of websites still works, and now it's GitHub's turn. Attackers have discovered that system administrators are as trusting as a child in a candy store. Just add an extra underscore to the URL, and you've got an entire IT team downloading a trojan. The worst part is that EtherRAT doesn't warn you: it doesn't pop up windows or ask for permissions. It simply installs itself, and while the technician boasts about their new tool, the attacker is already reviewing their passwords.