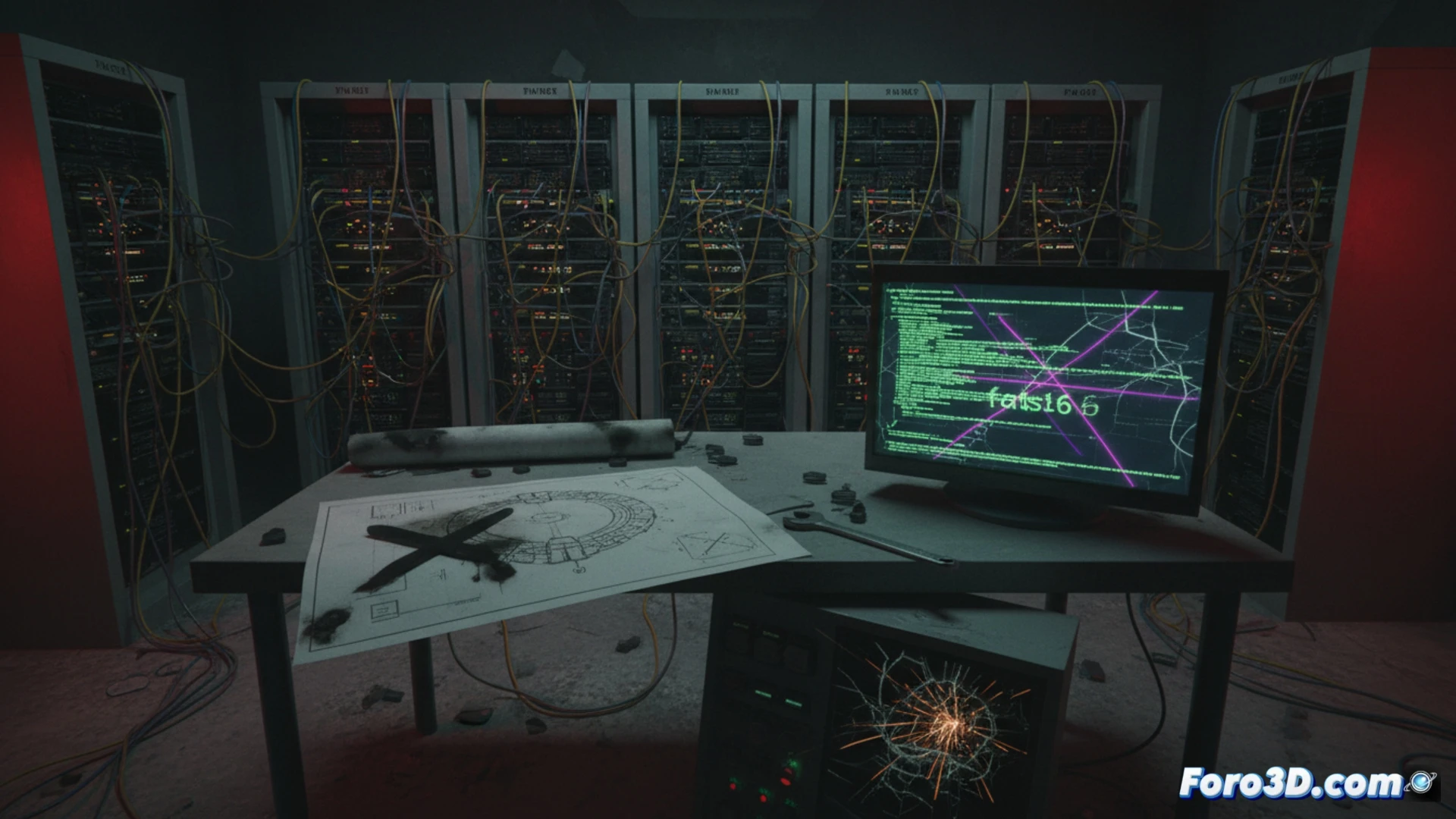
Researchers at SentinelOne have identified a cyberattack framework called fast16, created in 2005 and based on Lua, which preceded the famous Stuxnet worm. Its goal was to sabotage the Iranian nuclear program by manipulating high-precision calculation software, altering critical data to cause physical damage to uranium centrifuges.
Fast16: a silent attack on industrial processes 🛠️
The fast16 malware operated by interfering with industrial control systems, specifically altering the precision calculations necessary for uranium enrichment. Unlike Stuxnet, which spread more visibly, fast16 focused on modifying data without being detected, causing progressive equipment failures. Its Lua-based design allowed it to run lightly and adaptably, making it difficult to track in complex industrial environments.
When malware plays nuclear plumber 😅
It seems that the cyber attackers of 2005 already knew you don't need a hammer to break a centrifuge, just a well-written script. Fast16 demonstrates that before Stuxnet took all the fame, there were already malicious codes eager to act as digital plumbers. In the end, the real problem wasn't that the centrifuges spun fast, but that someone decided it was more fun to sabotage them than to play solitaire.