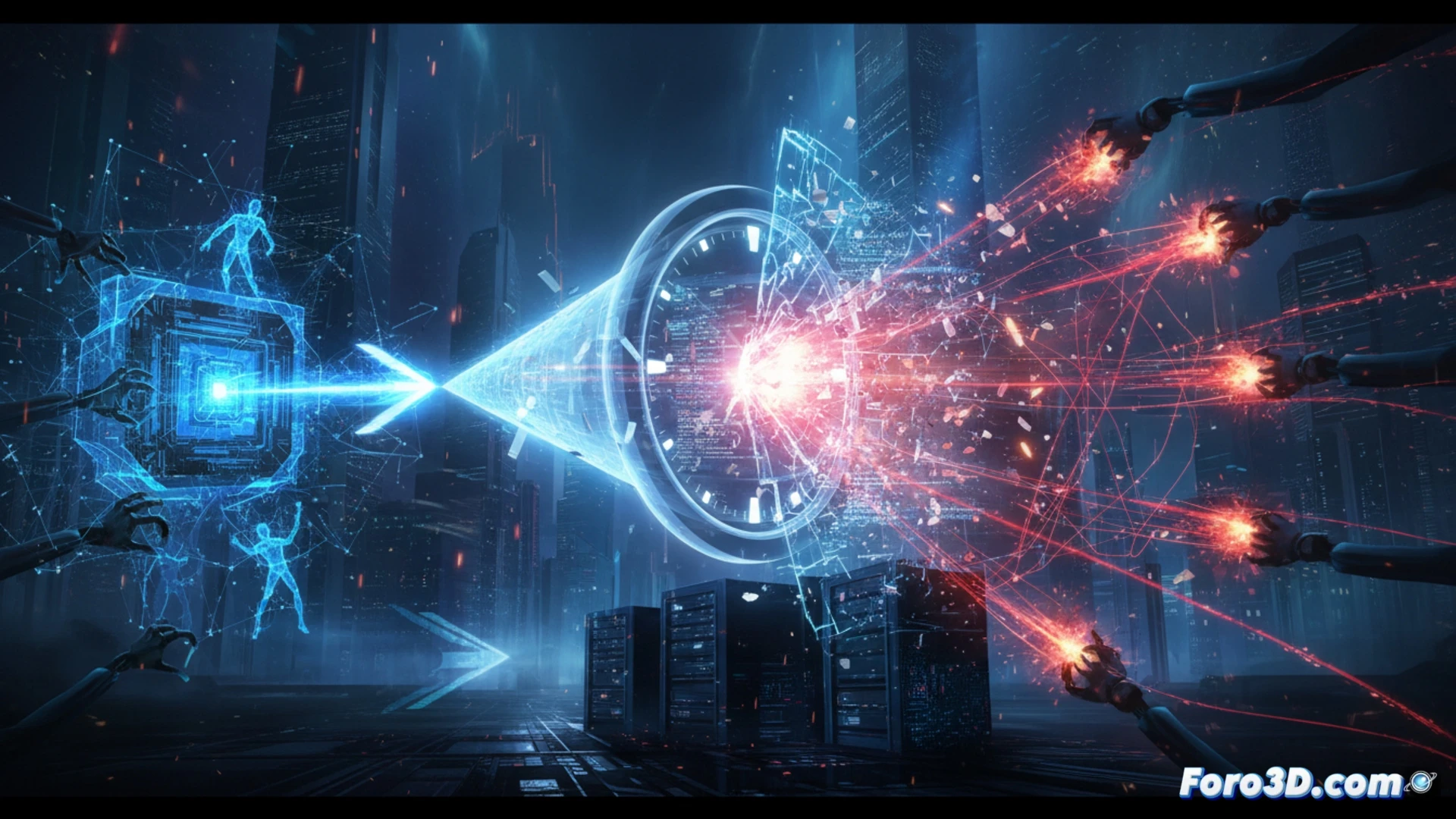
Artificial intelligence not only accelerates attacks; it collapses the window of time to react. Hackers automate vulnerability exploitation in seconds, rendering reactive defenses obsolete. This webinar addresses how cybersecurity must operate at the same pace as the threat, using automatic detection systems and real-time response to anticipate the exploit.
Defensive automation: machine learning against exploits 🛡️
The solution is not to patch faster, but to predict the vulnerability before it is used. Machine learning models trained on data from previous attacks identify anomalous patterns in traffic and system behavior. By integrating these systems with security orchestration, automation, and response (SOAR), a compromised service can be isolated or firewall rules applied in milliseconds, closing the door before the attacker finishes their request.
The myth of coffee while the firewall does its magic ☕
Sure, we can always trust that the administrator on duty will review the logs while sipping their morning coffee. The problem is that the exploit will have already executed, exfiltrated data, and erased its tracks before the first sip is finished. Reactive security is like closing the barn door after the horse not only escaped but also took the car. Defensive AI doesn't sleep, doesn't drink coffee, and above all, doesn't wait for you to finish your breakfast.