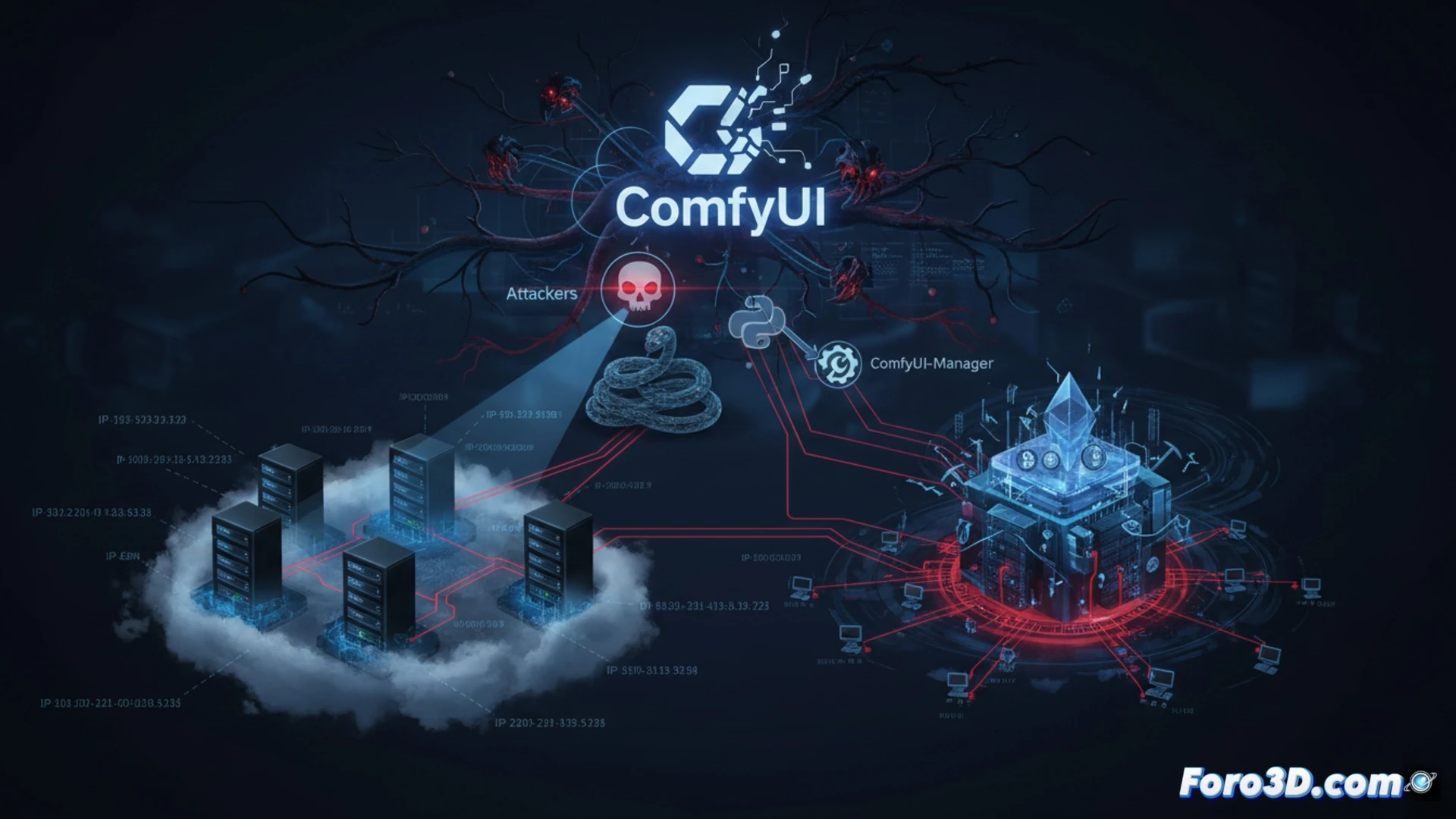
An active campaign is compromising servers with ComfyUI exposed on the internet. The goal is to integrate these machines into a botnet dedicated to cryptocurrency mining and to function as proxies. The attackers have managed to infiltrate over a thousand instances, taking advantage of the lack of basic security measures. This incident underscores the risks of deploying AI tools without proper configuration and network protection.
Infection Mechanism via ComfyUI-Manager 🔍
The attack uses a custom Python scanner that scans IP ranges of large cloud providers. When it locates an accessible ComfyUI instance, the malware is automatically deployed using the functionality of the ComfyUI-Manager extension. The script verifies that a malicious node is not already running before proceeding. Once installed, it hijacks the system's resources for the botnet, diverting its processing power towards illicit activities without the owner's knowledge.
Your GPU is Working Overtime for an Unknown Boss 😰
It's the dream of any idle resource: to be productive 24 hours a day. While you sleep, your graphics card works hard to solve complex mathematical problems, generating heat and electricity bills to make an anonymous blockchain enthusiast rich. All thanks to an overly helpful extension manager. Perhaps it's time to check if your ComfyUI is receiving unexpected visitors, before your hardware decides to ask for a raise in crypto.